I2P is a hidden layer of the Internet that facilitates decentralized, anti-censorship peer-to-peer communication. It keeps your online activity safe by encrypting it before being routed through a network of computers spread across the globe managed entirely by volunteers.
As an alternative to the Tor browser, I2P (Invisible Internet Project) is your best bet. I2P’s power lies in its efficiency- it is faster than Tor while still providing optimal hidden services.
Maintaining personal privacy is becoming more and more important in the modern digital world. It is important for all of us to take precautions to safeguard our privacy and security online, especially from invasive third parties like governments, hackers, and corporations. That’s why having the option to browse anonymously is useful.
If you value your privacy while online and wish to conceal your identity while surfing the web, Tor is probably the first thing that comes to mind.
But Tor has its drawbacks, and there are other alternatives out there, such as I2P. This article will examine I2P, its capabilities, and how it stacks up against Tor as an anonymous web browsing solution.
Contents
I2P: The Invisible Internet Project
The Invisible Internet Project (I2P) is a peer-to-peer system that emphasizes anonymity and decentralization. It was founded in 2002 with the goal of providing users with a private and anonymous alternative to the traditional internet. Since the code is open-source, anyone can access it and make changes as they see fit.
People use I2P to communicate with one another without fear of being monitored or having their data collected. Some people rely on it when they have to be discreet or when they are handling sensitive information.
Tor is like a disguise that helps you stay anonymous when you use the regular internet, while I2P is more like a secret club that has its own private internet where only invited members can go.
This means that I2P is home to its own set of proprietary services and programs that can only be accessed via the system itself. Among these are e-mail, instant messaging, file sharing, blogging, online forums, social media, and more. Using Outproxies, you can also access some Clearnet websites (the regular internet) via I2P.
Just how does I2P operate?
The system functions by recruiting users’ computers to act as “nodes” in a network that then routes data between itself and other nodes.
When you use it, it will break your data up into discrete packets and routes through a series of tunnels that connect various nodes.
Each node in the tunnel is aware of only the previous and next hops, but not the message’s source or final destination. Because of this, it is exceedingly difficult for anyone to monitor or intercept your communications.
Plus, it employs a more sophisticated form of onion routing called garlic routing. Using multiple layers of encryption keys, garlic routing encrypts a group of messages before sending them as a single packet. Since this eliminates unnecessary overhead and shields against correlation attacks, it is more secure and efficient than onion routing.
An eepsite (similar to a website) or an i2paddress is required to access I2P services and applications. These addresses are hashes of public keys encoded in base32, so humans can not read them like domain names.
Take, for instance: `http://i5q3w4x7kexej6nf55ufjnz4d4xmv6g5r3vnnx5zjnz25nur76ma.b32.i2p/`
is the address of the popular I2P search engine (Eepsite Search Engine).
Jump services (similar to URL shorteners) and naming services (similar to DNS) provide aliases for eepsite addresses to make them easier to remember and share.
Just as an illustration:
An alternative URL for the Eepsite Search Engine provided by the Jump Service is http://eepsites.i2p/.
How to Download, Install, and Use I2P?
This program is open source and free to use on any platform you like, including Windows, Linux, MacOS X, and Android.
You can get the software at https://geti2p.net/en/
I2P used to have a notoriously difficult installation process, but those days are long gone.
Now you can download a Windows-compatible build that doesn’t require the usual Java installation.
As a prerequisite to using I2P, all you need is Firefox or the Tor Browser Bundle.
After installation, we can use the program either as an application or as a service.
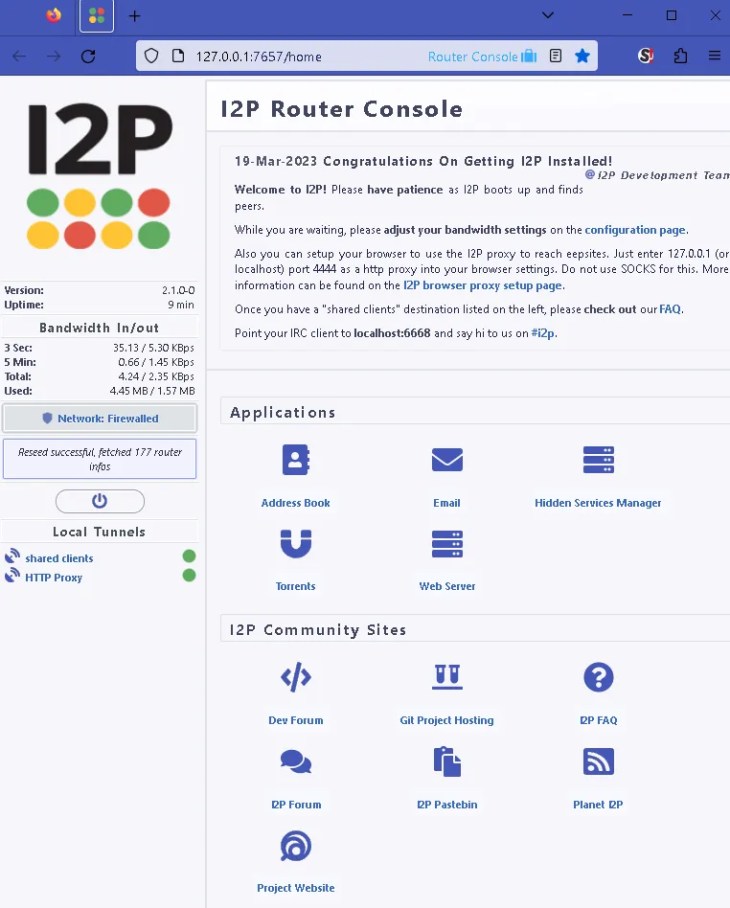
Upon installing the program, your computer will become an I2P router that can communicate with other nodes in the network.
When your router is up and running, you can log in to its web interface at http://127.0.0.0.1:7657/.
Through this user interface, you can change your router’s settings, check on the health of your network, oversee your tunnels, and gain access to a wide range of applications..
Unsurprisingly, the most tough part is actually locating I2P sites. “I2P Planet” (planet.i2p) is a popular starting point for users because it acts as an aggregator for trackers, blogs, and other similar feeds.
To some extent, “eepstatus” (identiguy.i2p) combines the functions of an index and a site status checker.
Last but not least, “Legwork” (legwork.i2p) is the closest thing to a conventional search engine.
However, you’ll probably encounter some sites that are down or that I2P merely says weren’t saved in your address book. To get the current B32 address, use a hop service.
That may sound complicated, but maintaining anonymity comes at a cost.
Although the I2P installer simplifies matters considerably, some manual labour is still required when navigating this darknet.
Why is I2P the best alternative to Tor?
While both are peer-to-peer networks with no central authority or user tracking, but they have several key differences. Here are a few of them:
Discover more from Techno360
Subscribe to get the latest posts sent to your email.




You must be logged in to post a comment.